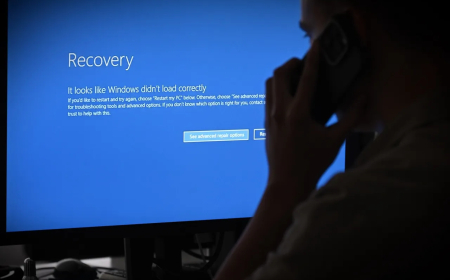
Hack-for-hire group exposed for targeting Android devices and iCloud backups
A hack-for-hire group has been caught targeting Android devices and iCloud backups, raising serious concerns about data privacy and cyber-espionage risks.

Security researchers have revealed the activities of a hack-for-hire group targeting journalists, activists, and government officials across the Middle East and North Africa. The attackers relied on phishing techniques to gain Access to VictAccessCloud backups and Signal messaging accounts, and deployed Android spyware capable of controlling compromised devices.
The campaign reflects a broader shift in the cyber-espionage landscape, where government agencies increasingly outsource hacking operations to private contractors. In many cases, authorities already depend on commercial spyware vendors that develop tools used by law enforcement and intelligence agencies to extract data from mobile devices.
Investigations conducted by Access Now identified at least three separate attacks between 2023 and 2025. The victims included two journalists from Egypt and one journalist in Lebanon, with the latter case also examined by SMEX. The incidents were further analysed by mobile cybersecurity firm Lookout. All three organisations collaborated on the research and published their findings in coordinated reports.
According to Lookout, the scope of the campaign extends beyond civil society figures in Egypt and Lebanon. Additional targets include individuals connected to government institutions in Bahrain and Egypt, as well as people in the United Arab Emirates, Saudi Arabia, the United Kingdom, and potentially the United States, including alums of American universities.
Researchers believe the group behind the attacks is linked to a hack-for-hire vendor with connections to BITTER APT, which cybersecurity experts have previously associated with the Indian government.
Justin Albrecht, a principal researcher at Lookout, indicated that the operation may be connected to an offshoot of the Indian startup Appin. He also pointed to a company named RebSec as a potential actor in the campaign. Earlier investigations published by Reuters in 2022 and 2023 examined Appin and similar firms, revealing how such organisations are allegedly hired to target executives, politicians, and military personnel.
Although Appin is believed to have shut down, Albrecht noted that the emergence of this campaign suggests that such activities have not disappeared but instead continued through smaller or restructured entities.
These hack-for-hire groups provide their clients with a degree of deniability by handling both operational execution and technical infrastructure. For customers, this approach can also be more cost-effective than acquiring high-end commercial spyware solutions.
Mohammed Al-Maskati, an investigator and director at Access Now’s Digital Security Helpline who contributed to the research, explained that these operations have become more accessible and difficult to attribute. He emphasised that identifying the end customer remains challenging because the infrastructure used in these attacks often obscures the responsible party.
While groups like BITTER may not possess the most advanced cyber tools, their methods remain highly effective. In this campaign, attackers used a range of techniques depending on the target’s device.
For iPhone users, the attackers attempted to trick victims into revealing their Apple ID credentials. By doing so, they could gain Access to iCloud, effectively exposing the full contents of the victim’s device. According to Access Now, this method can serve as a lower-cost alternative to deploying sophisticated iOS spyware.
For Android users, the attackers distributed spyware known as ProSpy. The malicious software was disguised as legitimate communication apps such as WhatsApp, Zoom, and Signal, as well as regionally popular apps like ToTok and Botim. Once installed, the spyware enabled extensive surveillance capabilities.
In certain cases, the attackers also used a technique to compromise Signal accounts. Victims were manipulated into linking a new device — controlled by the attackers — to their account, allowing the hackers to monitor communications. This method has been used by multiple threat actors, including groups associated with Russian intelligence operations. The findings highlight the growing sophistication and accessibility of cyber-espionage tools, as well as the increasing role of private actors in conducting targeted surveillance campaigns.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0