Exploit kit leak exposes potential vulnerability in millions of iPhones
A leaked exploit kit capable of targeting millions of iPhones raises serious concerns about security vulnerabilities, user privacy, and potential cyberattacks.

Cybersecurity researchers recently identified a hacking campaign aimed at iPhone users that relied on a sophisticated tool known as DarkSword. Shortly afterwards, a newer version of this tool was leaked and uploaded to the code-sharing platform GitHub, raising fresh concerns across the security community.
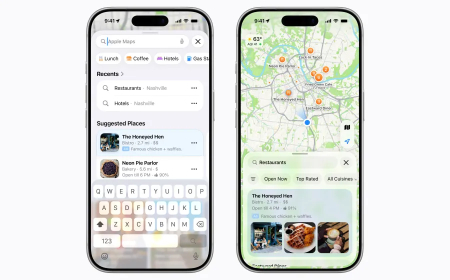
Experts warn that the public release of this exploit kit makes it significantly easier for attackers to target iPhone users, particularly those running older versions of Apple's operating systems who have not yet upgraded to iOS 26. Based on Apple's own data regarding devices still running outdated software, the number of potentially affected iPhones and iPads could reach into the hundreds of millions.
"This is bad. They are way too easy to repurpose," said Matthias Frielingsdorf, co-founder of mobile security company iVerify. He added that the situation may be difficult to control and that malicious actors are likely to begin deploying these tools more widely.
According to Frielingsdorf, the newly leaked versions of DarkSword share the same underlying infrastructure as earlier variants analysed by iVerify, though there are slight differences in the files. He noted that the code published on GitHub is relatively simple, consisting mainly of HTML and JavaScript, which allows it to be easily copied and hosted on a server within a short time frame.
"The exploits will work out of the box," he explained, emphasising that no specialised knowledge of iOS is required to use them.
Google researchers have reached a similar conclusion. Kimberly Samra, a spokesperson for the company, confirmed that their analysis aligns with concerns that the exploit is easy to deploy. A security enthusiast known online as matteyeux also demonstrated the tool's practicality, reporting that they successfully compromised an iPad mini running iOS 18 using one of the leaked samples circulating online.
Apple has acknowledged the issue. Company spokesperson Sarah O'Rourke stated that Apple is aware of the exploit affecting devices running outdated operating systems and had already issued an emergency security update on March 11 for devices unable to upgrade to newer iOS versions. She stressed that keeping software updated is the most effective way to maintain device security and added that devices running current software versions are not vulnerable to these attacks. She also noted that enabling Lockdown Mode can help block such exploits.
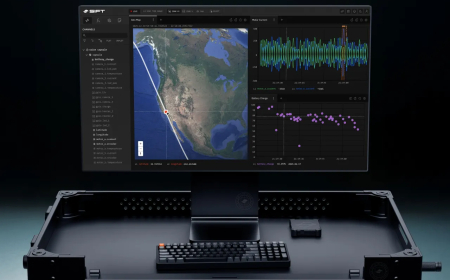
Details in the leaked files suggest the tool can extract sensitive information from compromised devices. One comment, believed to have been written by a developer involved in DarkSword, describes how the exploit can access and transmit forensic data from iOS devices over the internet to attacker-controlled servers.
Additional code references outline post-exploitation activities, including collecting data such as contacts, messages, call history, and information stored in the iOS keychain (which contains Wi-Fi credentials and other sensitive details), and transferring it remotely.
Another file mentions uploading data to a Ukrainian apparel website, though the reason for this remains unclear. Previous reports have indicated that DarkSword may have been used by Russian state-linked hackers targeting Ukrainian entities.
Security firms,s including iVerify, Google, and Lookout,t have confirmed that this spyware specifically targets devices running iOS 18. Apple's statistics indicate that roughly one-quarter of iPhone and iPad users are still on iOS 18 or earlier. With more than 2.5 billion active Apple devices globally, a significant number of users could be at risk.
Given these findings, Frielingsdorf advises all users to update their devices to the latest available operating system as soon as possible.
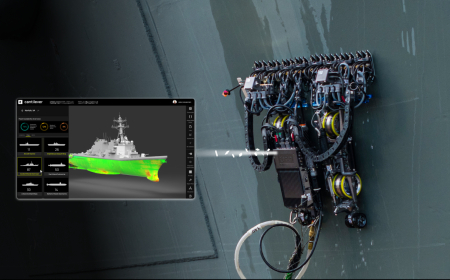
The emergence of DarkSword comes shortly after the discovery of another advanced iPhone exploitation toolkit known as Coruna. Defence contractor L3Harris reportedly developed that tool through its Trenchant division, which develops hacking technologies for U.S. government agencies and their allies.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0