CISA warns firms to secure Microsoft Intune after hackers wipe Stryker devices
CISA urges companies to secure Microsoft Intune systems after hackers wiped thousands of Stryker devices, raising concerns over enterprise endpoint security risks.

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning to organisations, urging them to strengthen the security of systems that manage employee devices after a cyberattack on the medical technology company Stryker that wiped thousands of devices.
According to CISA, pro-Iran hackers gained access to Stryker’s systems. They used that access to compromise its Windows-based network, ultimately misusing its endpoint management tools to disrupt operations globally. The agency confirmed on Thursday that it is aware of how the attackers leveraged these systems to carry out the attack.
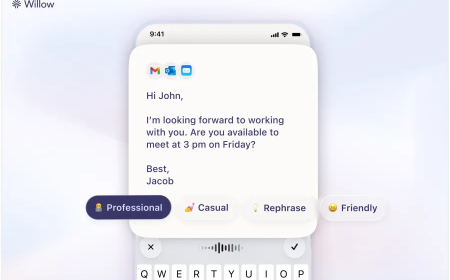
CISA advised that organisations should implement stricter controls on administrative accounts with access to device management platforms, such as Microsoft Intune, which Stryker uses to manage employee devices remotely. In particular, the agency recommended requiring secondary approval for high-impact actions, such as remotely wiping devices, to prevent unauthorised or malicious use.
Stryker, which produces medical equipment for hospitals, disclosed on March 11 that it had experienced a cyberattack that caused widespread disruption across its network. The company stated that the attackers did not deploy traditional malware or ransomware. Instead, reports indicate that the hackers used their access to Stryker’s internal systems to manipulate its Intune dashboards and remotely erase data from tens of thousands of employee devices, including personal phones and computers connected to the network.
The company has since reported that it has contained the incident and is working to restore its systems. While its medical devices remain functional, Stryker noted that key operational systems related to supply, ordering, and shipping are still offline.
Stryker has not provided a timeline for when full recovery will be completed, and the company did not respond to requests for additional comment.
A group identifying itself as Handala, described as pro-Iran hacktivists, claimed responsibility for the attack. The group said the breach was carried out in response to a U.S. airstrike in Iran that reportedly resulted in civilian casualties, including children. The attackers also claimed to have obtained significant amounts of data from Stryker’s network, but have not presented evidence to support the claim.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0