Cisco warns hackers have abused critical vulnerability to access major customer networks since 2023
Cisco confirms that attackers have been exploiting a critical security flaw since 2023 to gain unauthorised access to large enterprise customer networks.

Cisco says hackers have been exploiting a flaw in one of its widely used networking products for large enterprises for at least three years, prompting warnings from the U.S. government and several allies urging organisations to respond quickly.
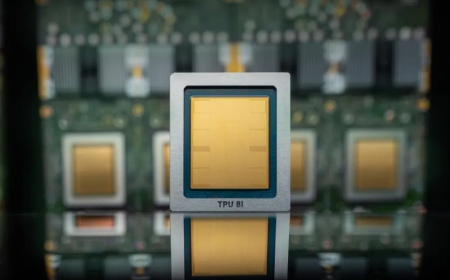
The vulnerability, which carries a maximum severity score of 10.0, affects Cisco’s Catalyst SD-WAN products, which are used by major companies and government agencies with multiple locations to connect private networks over long distances. According to Cisco, the bug can allow attackers to compromise exposed systems running the affected SD-WAN technology remotely.
By exploiting the issue over the internet, attackers can obtain the highest level of privileges on the impacted devices and maintain persistent, concealed access inside a victim’s environment. That type of foothold can enable long-term spying, monitoring, or data theft across an organisation’s network.
Cisco said that after identifying the vulnerability, its researchers found evidence suggesting exploitation dates back to 2023. Some of the affected organisations are believed to be part of critical infrastructure. Cisco did not name specific victims, but the term “critical infrastructure” can encompass sectors such as energy, water systems, and transportation.
A joint government alert issued by several countries — including Australia, Canada, New Zealand, the United Kingdom, and the United States — warned that threat actors are targeting organisations “globally.”
In the U.S., the Cybersecurity and Infrastructure Security Agency (CISA) directed all civilian federal agencies to patch by the end of the day on Friday, citing an imminent threat and an unacceptable risk to federal systems. CISA, currently operating with reduced capacity due to a partial government shutdown, said it is aware of active exploitation.
Neither Cisco nor the governments issuing the alerts linked the activity to a specific hacking group or nation-state actor. Still, one cluster of activity has been tracked under the label UAT-8616.
In December, Cisco issued a separate warning about another maximum-rated 10.0 vulnerability in the Async software that powers many of its products — a flaw that was also being actively exploited to break into customer networks.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0