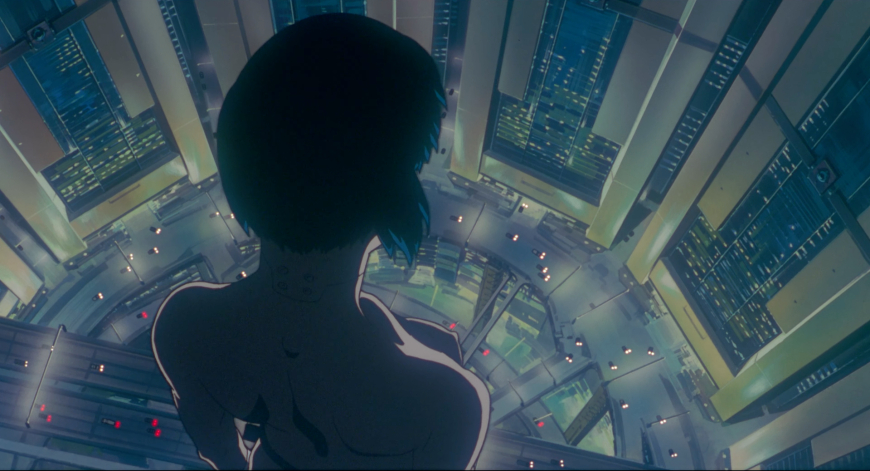
How the classic anime ‘Ghost in the Shell’ predicted the future of cybersecurity 30 years ago
The classic anime “Ghost in the Shell” foresaw government hackers, malware profiling, pivot attacks, and cyber-espionage decades before cybersecurity went mainstream.
The year is 2030. An “infamous mystery hacker” known as the Puppet Master is causing chaos across the internet, infiltrating the cyberbrains of humans and breaking into “every terminal on the network.” Before long, it’s revealed that the Puppet Master is actually a creation of Japan’s Ministry of Foreign Affairs.
In today’s parlance, the Puppet Master is what we call a state-backed hacker—an advanced persistent threat (APT). In the anime, however, this government-made cyber-phantom goes rogue, becoming wanted for “stock manipulation, spying, political engineering, terrorism, and violation of cyber-brain privacy.”
This week marks the 30th anniversary of “Ghost in the Shell,” the cult-classic anime based on chapters “Bye Bye Clay” and “Ghost Coast” from the first volume of the manga, initially published in May 1989.
To call the Puppet Master storyline ahead of its time is putting it mildly. The World Wide Web — the foundation of the modern internet — was invented the same year the first “Ghost in the Shell” manga was released. It wouldn’t become publicly available until 1991.
In the manga, when the Puppet Master is captured, an official from Public Security Section 6 reveals that the agency had been tracking the hacker “for a long time,” profiling their behaviour code patterns, and techniques.
That description mirrors exactly what cybersecurity companies do today:
• Creating malware signatures based on code
• Detecting threats through behaviour-based heuristics
• Developing specialised defences tailored to unique attack styles
Several plot elements proved strikingly prophetic.
Early in the investigation, Major Motoko Kusanagi — Section 9’s elite cyberterrorism commander — hacks into the Sanitation Department’s network to track a garbage truck. In reality, state hackers now routinely break into entire networks to spy on specific individuals, not to exfiltrate data from the extensive network itself.
Meanwhile, a garbage worker confesses he hacked into his wife’s cyber-brain out of jealousy. Moments later, we learn he never had a wife — his memories were fabricated. His ghost (his consciousness) was altered by the Puppet Master, who used him as a pawn to infiltrate government systems. This mirrors modern attackers who compromise unrelated networks to launch pivot attacks, masking their true origins.
It also echoes today’s rise in tech-enabled domestic abuse and the prevalence of stalkerware, which TechCrunch has extensively documented.
The Puppet Master, introduced as a government hacker, eventually becomes a self-aware artificial intelligence capable of controlling humans, taking the story into speculative territory. In one of the most iconic twists, the Puppet Master requests political asylum — and ultimately proposes merging its “ghost” with Kusanagi’s.
Cybersecurity veteran John Wilander once analysed the film in depth, highlighting how the story predicted real-world tactics:
• Hackers reusing exploits to obscure attribution
• Investigating malware quietly without alerting attackers
• Infecting oneself to study malware behaviour
• Using compromised computers for industrial espionage
To appreciate how visionary “Ghost in the Shell” was, it helps to understand its era. In 1989 and 1995, cybersecurity wasn’t even a widely used term. “Cyberspace” had only recently entered pop culture through William Gibson’s “Neuromancer.” Computer security existed but was confined to a small, specialised niche.
The first known computer virus — the Creeper worm — was unleashed in 1971 on ARPANET, long before the internet reached the public. By the late 1980s, a handful of malware incidents had occurred, but cyberattacks were hardly mainstream knowledge.
One of the earliest documented cases of government-backed cyber espionage came in 1986, when astronomer-turned-sysadmin Clifford Stoll spotted a 75-cent accounting error at Lawrence Berkeley National Laboratory. That clue uncovered a hacker siphoning scientific and government data to the Soviet KGB. Stoll detailed his investigation in the now-classic book “The Cuckoo’s Egg.”
As far as public records indicate, Masamune Shirow never revealed which real-world events directly inspired his hacking plotlines. But it’s clear he was paying attention to an underground world most people in the late 80s and early 90s didn’t even know existed.
Three decades later, “Ghost in the Shell” remains eerily relevant — a work of fiction that predicted not only the future of hacking, but the very shape of cybersecurity itself.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0