Russians accused of using advanced iPhone hacking tools to steal Ukrainian personal data
Investigators say Russian-linked groups used advanced iPhone exploits to access the personal data of Ukrainians, raising concerns over mobile security and cyber warfare tactics.
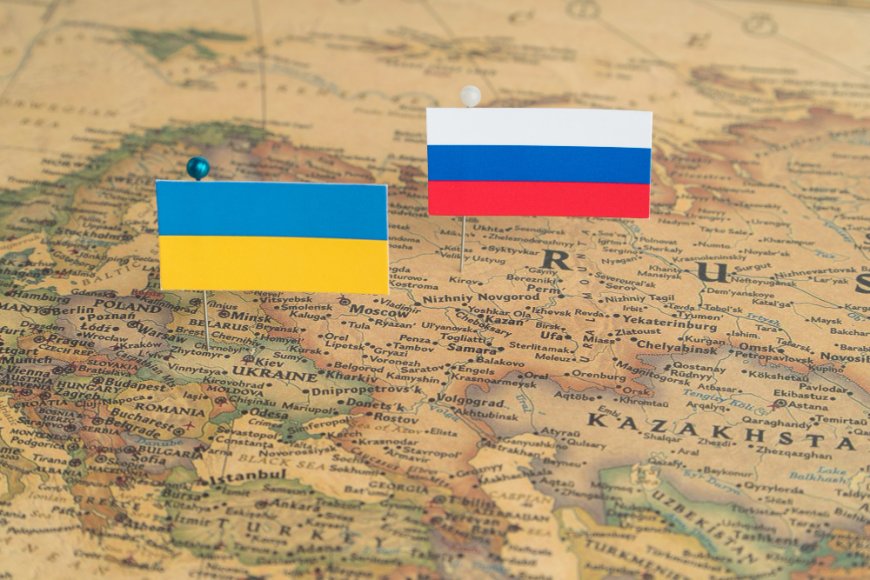
A group of hackers believed to be at least partially linked to the Russian government has targeted iPhone users in Ukraine with a sophisticated set of hacking tools to extract personal data and potentially steal cryptocurrency, according to cybersecurity researchers.
Experts from Google, along with researchers at iVerify and Lookout, examined recent cyberattacks against Ukrainian users carried out by a group identified as UNC6353. Their investigation focused on compromised websites involved in a campaign that appears connected to another operation uncovered earlier this month. In this latest wave, attackers deployed a hacking toolkit referred to as Darksword.
The identification of Darksword, following the earlier discovery of a similar toolkit, suggests that advanced, stealthy spyware targeting iPhones may be more widespread than previously assumed. However, this particular campaign appears to have been limited to Ukrainian users, suggesting a more controlled scope rather than a global attack.
Earlier in March, Google disclosed details about another advanced iPhone exploitation toolkit known as Coruna. According to the company, that tool was initially used by a government client of a surveillance technology vendor, later adopted by Russian operatives targeting Ukrainian individuals, and eventually used by Chinese cybercriminals seeking to steal cryptocurrency. The toolkit was originally developed by U.S. defence contractor L3Harris, specifically within its hacking and surveillance division, Trenchant.
Coruna was reportedly intended for use by Western governments, particularly members of the Five Eyes intelligence alliance, which includes Australia, Canada, New Zealand, the United States, and the United Kingdom, according to former employees familiar with L3Harris’ work on iPhone exploitation tools.
In the latest findings, researchers identified a related campaign using updated hacking tools that exploit different vulnerabilities. The Darksword toolkit is designed to collect sensitive information, including passwords, photos, messages from apps like WhatsApp and Telegram, standard text messages, and browsing history. Unlike persistent surveillance tools, Darksword is structured for short-term access—infecting devices, extracting data quickly, and then disappearing.
According to Lookout researchers, the malware’s presence on a device likely lasts only minutes, depending on how much data it gathers and transmits.
Rocky Cole, co-founder of iVerify, suggested that the attackers were likely interested in understanding users’ behaviour patterns rather than maintaining continuous surveillance, making the approach more of a rapid “smash-and-grab” operation.
The toolkit also includes functionality for stealing cryptocurrency from commonly used wallet applications, which is somewhat unusual for a group suspected of having state backing. Lookout noted that this could indicate either a financial motive or an expansion of state-aligned operations into financial theft targeting mobile devices.
However, Cole pointed out that there is no direct evidence showing the group actively pursued cryptocurrency theft, only that the capability exists within the malware.
Researchers also observed that the malware was professionally engineered, featuring a modular design that allows additional functions to be integrated easily. This level of sophistication suggests it was developed with significant resources. Cole added that the same individual or entity that provided Coruna to Russian-linked operators may also have supplied Darksword.
Regarding attribution, Cole stated that the available evidence strongly points toward involvement by the Russian government. At the same time, Lookout concluded that the same group behind the Coruna campaign is likely responsible for the Darksword attacks.
“UNC6353 is a well-funded and connected threat actor conducting attacks for financial gain and espionage in alignment with Russian intelligence requirements,” said Justin Albrecht, principal security researcher at Lookout. “We believe that a case can be made that UNC6363 is potentially a Russian criminal proxy, given the dual goals of financial theft and intelligence collection.”
As for how victims were targeted, Cole explained that the malware was designed to infect anyone who accessed certain Ukrainian websites while physically located in Ukraine. This indicates the campaign was not highly selective but rather opportunistic within a defined geographic scope.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0