Stryker begins system recovery after pro-Iran hackers erase thousands of employee devices
Stryker is restoring systems after a cyberattack by pro-Iran hackers wiped thousands of employee devices, raising concerns over healthcare cybersecurity risks.

Medical technology company Stryker is restoring its systems after a cyberattack that reportedly enabled pro-Iranian hackers to remotely wipe data from tens of thousands of employees' devices.
The breach caused widespread disruption to the company's operations and is believed to be the first major cyberattack in the United States linked to the Trump administration's war in Iran.
In an update over the weekend, Stryker said the March 11 incident was contained within its internal Microsoft environment and added that its internet-connected medical devices remain "safe to use." The company noted that while the investigation is ongoing, there is no evidence of ransomware or malware. However, its ability to process orders, manufacture, and ship products remains affected.
A hacking group known as Handala claimed responsibility, stating the attack was retaliation for a U.S. airstrike on an Iranian school that reportedly killed at least 175 people. The group also defaced Stryker's login pages.
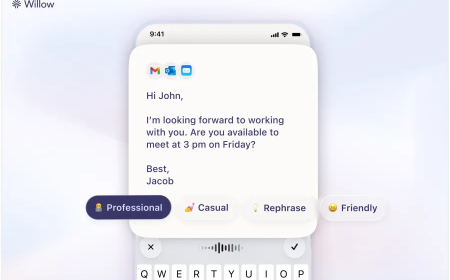
According to reports, the attackers may have gained access through an internal administrator account, giving them broad control over Stryker's Windows network. They allegedly accessed Microsoft Intune systems, which are used to manage employee devices remotely, including the ability to wipe data. This access could have enabled them to erase data from company and personal devices without deploying malware.
It remains unclear how the attackers initially breached the network. Security researchers suggest phishing may have been used, while others point to possible credential theft through infostealer malware. Groups linked to Iran have previously used similar tactics and have targeted sectors including healthcare and energy.
Stryker, which employs around 56,000 people across more than 60 countries, has not yet commented on whether the compromised account was protected with multi-factor authentication.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0