These Are the Cybersecurity Stories We Were Jealous of in 2025
As 2025 comes to a close, a curated selection of standout cybersecurity journalism highlights the most compelling stories the industry produced this year. From government surveillance revelations to major hacking investigations, these reports showcase the impact and importance of in-depth cybersecurity reporting.

As the year comes to a close, it's time to look back and celebrate some of the best cybersecurity stories that we didn't publish ourselves. Since 2023, TechCrunch has made it a tradition to highlight standout reporting from across the cybersecurity world.
The idea is simple. Dozens of journalists now cover cybersecurity, privacy, and surveillance in English, producing a substantial volume of reporting each week. Many of those stories are excellent and deserve attention. This list is a subjective and incomplete selection of the ones we admired most this year — and that we think you should read.
Let's dive in.
— Lorenzo Franceschi-Bicchierai
Shane Harris chronicled his relationship with a senior Iranian hacker who was later killed.
Every so often, a hacker story reads as if it belongs on the big screen—that's the case with Shane Harris's deeply personal account of his months-long correspondence with a senior Iranian hacker.
In 2016, the Atlantic journalist was contacted by someone claiming to work for Iran's intelligence services. The source said he had taken part in primary operations, including the downing of a U.S. drone and the destructive cyberattack on Saudi Aramco that wiped company computers. Harris was initially sceptical, but over time — and after the hacker revealed his real name — the story began to hold up.
After the hacker's death, Harris pieced together what truly happened, uncovering a story that proved even more remarkable than the source's original claims. The piece also offers a rare behind-the-scenes look at the risks and challenges cybersecurity reporters face when dealing with sources who claim insider access.
The Washington Post exposed a secret U.K. order demanding Apple enable surveillance.
In January, the U.K. government secretly served Apple with a court order requiring the company to create a backdoor that would allow authorities to access iCloud data for any customer worldwide.
Because the order included a global gag provision, the public learned of it only after The Washington Post broke the story. The demand marked a historic escalation in government surveillance efforts and posed a serious threat to encryption practices that tech companies have spent years defending.
In response, Apple halted its opt-in end-to-end encrypted cloud storage offering in the U.K. The reporting triggered widespread scrutiny of British surveillance powers and sparked a months-long diplomatic dispute between the U.K. and the U.S. Eventually, the request was withdrawn — only for officials to attempt a similar move later.
"The Trump administration accidentally texted me its war plans" delivered the year's best headline
Few journalists ever get accidental access to history unfolding in real time. That's precisely what happened to The Atlantic's editor-in-chief, Jeffrey Goldberg, after he was mistakenly added to a Signal group chat involving senior U.S. officials discussing military operations.
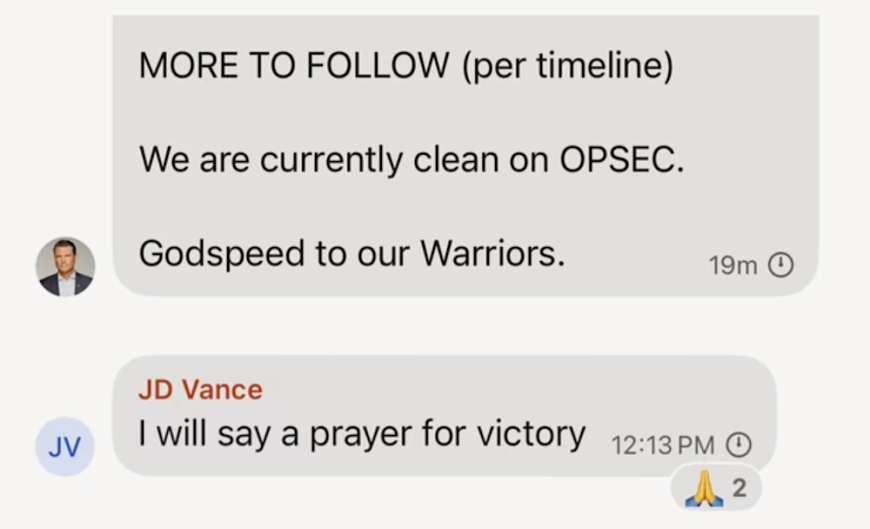
"We are currently clean on OPSEC," said Secretary of Defence Pete Hegseth. They were not. Image Credits: The Atlantic (screenshot)
Goldberg watched as messages about bombing targets were exchanged — and then confirmed their authenticity as news reports described strikes happening abroad. Realising the gravity of what he had seen, Goldberg reported the story, setting off a months-long investigation into government operational security failures.
The fallout exposed widespread lapses, including the use of a Signal knock-off app that further compromised supposedly secure communications, in what many called one of the most significant government opsec failures in history.
Brian Krebs identified a prolific hacker group administrator as a Jordanian teenager.
Veteran cybersecurity journalist Brian Krebs has built a career out of unmasking cybercriminals by following digital breadcrumbs. In one of this year's most impressive investigations, Krebs revealed the real-world identity behind the online alias "ey," an administrator in the cybercrime group known as Scattered LAPSUS$ Hunters.
Krebs went beyond identification, speaking with someone close to the hacker nd eventually the hacker himself. The teenager admitted to his crimes and said he was trying to leave the cybercriminal world behind, adding a human dimension to a story about online crime.
Airlines shut down a massive surveillance program following 404Media's reporting.
Independent outlet 404 Media delivered some of the most impactful journalism of the year, despite having far fewer resources than mainstream organisations.
One of its major revelations was a sweeping air travel surveillance program operated by the Airlines Reporting Corporation, a data broker created by the airline industry. The organisation was selling access to data from billions of airline tickets—including passenger names and financial details—to U.S. government agencies without warrants.
Following months of reporting and mounting pressure from lawmakers, ARC announced it would shut down the program. The episode demonstrated how determined reporting can force real-world change.
Wired built a 3D-printed gun to examine the reality of "hghostguns"
After the December 2024 killing of UnitedHealthcare CEO Brian Thompson, attention quickly turned to allegations that the suspect used a 3D-printed "h ost gun"— a firearm without serial numbers built outside the background-check system.
Wired drew on its years of reporting on 3D-printed weapons to investigate how accessible such firearms really are. The outlet documented the process of building one while navigating the complex legal and ethical terrain surrounding ghost guns. The resulting reporting — and accompanying video — was both methodical and unsettling.
NPR reported on a whistleblower who exposed DDOS's access — and faced threats
The Department of Government Efficiency, or DOGE, dominated headlines in 2025 as Elon Musk–aligned operatives dismantled security safeguards across federal agencies to obtain vast datasets on U.S. citizens.
NNPR's reporting stood out, particularly a story detailing a whistleblower's disclosure to Congress. A senior IT employee at the National Labour Relations Board said that while investigating DDOGE's actions, he found an envelope taped to his door containing threats, personal information, and surveillance photos of him walking his dog.
The reporting highlighted the personal risks faced by government employees who try to resist mass data collection.
Mother Jones uncovered a massive dataset tracking surveillance victims worldwide.
Any article that begins with a journalist admitting they felt physically sick after a discovery is bound to be compelling. GabrieGGeiger's reporting for Mother Jones revealed a dataset from a little-known surveillance company called First Wap.
The records detailed phone location tracking from 2007 to 2015 and included data on thousands of people worldwide. Geiger identified tracked individuals ranging from a former Syrian first lady to a Vatican adversary and a Hollywood actor. The investigation revealed that the SS7 telecommunications protocol has long enabled covert global surveillance.
Wired traced the investigation behind a wave of nationwide "waging" attacks.s
Swatting — falsely reporting violent crimes to trigger armed police responses — has evolved from a prank into a lethal threat. In one of this year's most comprehensive features, Wired's Andy Greenberg examined the people and systems behind hundreds of swatting incidents targeting schools across the U.S.
The story profiled emergency call operators, victims, a prolific swatter known as Torswats, and even a hacker who independently tracked the suspect. The reporting humanised a complex problem and exposed vulnerabilities in public safety systems.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0