Kaspersky links suspected Chinese hackers to a backdoor attack involving Daemon Tools
Kaspersky suspects Chinese hackers inserted a backdoor into Daemon Tools during a widespread cyberattack, raising major cybersecurity concerns.

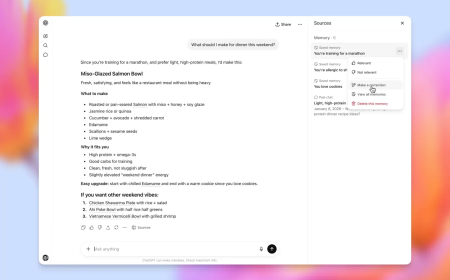
Security researchers at Kaspersky say they have uncovered a malicious backdoor embedded in the widely used Windows disc imaging software Daemon Tools.
The Russian cybersecurity firm said on Tuesday that telemetry data collected from systems running its antivirus software indicates a “widespread” attack is currently underway, affecting thousands of Windows computers that use Daemon Tools.
According to Kaspersky, the attackers — believed to be a Chinese-speaking threat group based on malware analysis — leveraged a backdoor in Daemon Tools to deploy additional malicious payloads across a dozen systems. These targeted systems span industries including retail, scientific research, manufacturing, and government infrastructure. The company noted that the selection of victims suggests a highly “targeted” campaign.
The affected organisations are located in Russia, Belarus, and Thailand.
Kaspersky reported that the backdoor activity was first detected on April 8.
The firm also said it had notified Disc Soft, the developer behind Daemon Tools, though it did not confirm whether the company responded or implemented mitigation steps. According to Kaspersky, the supply chain attack remains “still active,” suggesting that attackers may continue distributing malware through the compromised software to a large number of users.
This incident adds to a growing list of supply chain attacks targeting widely used software providers. In such attacks, hackers compromise developer environments or distribution channels to inject malicious code into legitimate software updates, enabling them to infiltrate many systems simultaneously.
Earlier this year, attackers linked to the Chinese government reportedly compromised the popular text editor Notepad++ to distribute malware to organisations connected to East Asia. More recently, researchers warned of another incident involving users who visited the website of CPUID, the company behind widely used tools like HWMonitor and CPU-Z.
Further analysis revealed that after downloading the Windows installer directly from the Daemon Tools website, the file appeared to contain the backdoor when scanned using the online malware detection service VirusTotal.
It remains unclear whether the macOS version of Daemon Tools has also been compromised or if other applications developed by Disc Soft are affected. When asked for comment, a representative from Disc Soft stated that the company is “aware of the report and is currently investigating the situation.”
“Our team is treating this matter with the highest priority and is actively working to assess and address the issue. At this stage, we cannot confirm the specific details referenced in the report. However, we are taking all necessary steps to remediate any potential risks and to ensure the security of our users,” the representative said.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0